Transaction fraud and how to detect it
The world is no longer restricted by geography; the rise of the digital economy has bought about the creation of a global network of individuals and businesses and the services we offer each other. Digital transactions connect us to this network and facilitate exchange, and while this creates enormous eCommerce opportunities it also brings new threats and challenges.
Building trust in this digital world is a prerequisite to business success. Now trade has moved beyond the groups of people we know personally, transacting online requires identity verification and identity proofing (often referred to as ‘know your customer’ in regulated industries) at the initial stage of onboarding customers to services, before transactions can take place.
“Transaction fraud describes the attempt to deliberately seek financial or other personal gain through wrongful or criminal deception.”
Beyond onboarding, businesses must continue to protect themselves and their customers from bad actors and fraudulent activity as transactions occur. The ability to sift transaction events, segregate and identify suspicious activities or anomalies in an intelligent way, and generate accurate, efficient and timely feedback on the analysis of transactions is essential to maintaining an excellent customer experience and ensuring business success.
What is transaction fraud?
Transaction fraud is a risk for any business trading online. It describes the attempt to deliberately seek financial or other personal gain through wrongful or criminal deception. This deception might include the misappropriation of identity or payment methods or the misrepresentation of information by a fraudster or a customer.
Transaction fraud committed by organised criminals tends to victimise unsuspecting individuals. Transaction fraud perpetrated by customers and targeting businesses, on the other hand, seeks to abuse customer care return policies and chargeback procedures designed to provide legitimate support.
In the first half of 2022, criminals stole a total of £609.8 million through authorised and unauthorised fraud and scams and fraud types continue to increase.
Track digital transactions across all channels and stop fraud before it happens
Transaction fraud comes in many forms and evolves quickly as fraudsters seek new ways to exploit digital vulnerabilities. The following broad categories of transaction fraud each contain a growing list of specific fraud typologies:
Authorised fraud
This type of transaction fraud tricks or coerces a victim into initiating a payment. Methods include, purchase scams, investment scams, romance and advance fee scams, invoice and mandate fraud, CEO fraud and impersonation. These scams tend to rely on social engineering, fake phone calls, text messages, emails, websites and social media posts to lure and target victims.
Authorised push payment (APP) fraud
This fraud attempts to convince, or ‘socially engineer’, a victim to send a payment to an account controlled by the criminal. Posing as a legitimate authority, such as, a government department, bank or debt collection agency, the fraudster creates a false sense of urgency intended to elicit an immediate payment in response.
The most sophisticated authorised push payment frauds attempt to legitimise their approach by feigning association with a service used by the victim, such as a utility company, broadband provider or online store. Hacked or intercepted account information is used to create the deception of an existing relationship with the potential loss of service used as emotional leverage.
Unauthorised fraud
The other type of money transfer fraud involves payments made without the victim’s consent. This generally covers account takeover (ATO) and internal fraud.
This type of fraud is often carried out via phishing emails, fake call centres, device compromise and SIM swap, malware and identity spoofing.
Account takeover (ATO) fraud
Account takeover is a type of identity theft and a very common type of transaction fraud. It hinges on the theft or interception of personal account credentials, security questions and other data useful to gain account access.
How does account takeover work?
Step 1. Data
A fraudster acquires stolen details via social engineering, malware or the dark web.
Step 2. Access
The fraudster gains account access, either directly or indirectly via a customer service call centre by learning the verification checks and responses.
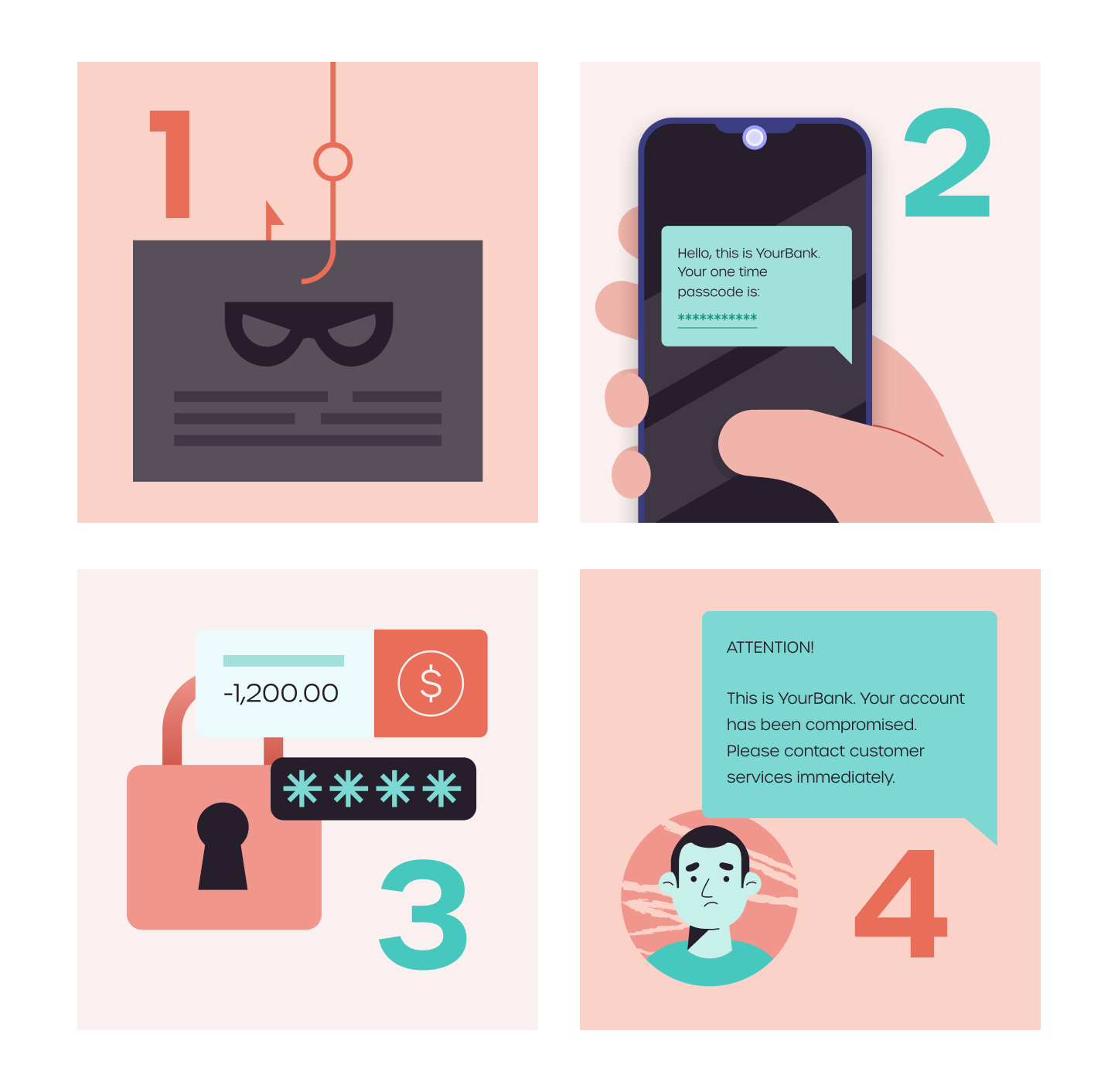
Step 3. Fraud
The fraudster transfers value out of the account and changes account access.
Step 4. Discovery
The victim learns of loss of account access from a security notification or statement and must begin what is often a long and difficult process of regaining control of the account via customer services.
Like other forms of money transfer fraud, social engineering is used to manipulate victims into releasing sensitive information or making security mistakes that permit access to their device. These tricks pray on a victim’s willingness to help or deference to authority and are often driven by perceived time sensitivity.
Personal data, obtained from a breach or leak, can also be purchased via the dark web. Typically graded for quality, freshness and detail, premium data is even tested and verified to ensure its value to a fraudster.
Identity theft
Identity theft involves the fraudulent use of another person’s personal identity data without their consent and is a potential threat across the customer lifecycle from new customer onboarding to in-life transaction events, such as payments.
Stolen data can range from personally identifiable information (PII), such as name, address and date of birth right up to ID documents with a much wider scope for assuming or hijacking an individual’s identity. Unauthorised email access is a common gateway to multiple user accounts associated with that address, leading to account takeover and developing into wider identity control.
“Creating a feedback loop between onboarding and transaction events enables end-to-end customer risk mitigation across the customer lifecycle.”
Sleeper fraud
Sleeper fraud is one of the most challenging forms of emerging fraud. Criminals playing a long game open accounts and complete legitimate transactions to gradually build their credit rating and acquire access to greater funds. Once in a position to maximise the value of a loan, withdrawal or transfer, the fraudster exploits the opportunity to cash in and disappear with the proceeds.
‘Bust-out-fraud’ is a speedier deception that leverages similar techniques, but typically targets products and services offering faster access, such as credit cards, personal loans and increasingly Buy Now Pay Later products.
Card payment fraud
Card not present
Sometimes referred to as ‘remote purchase fraud’, this type of card payment fraud makes unauthorised use of stolen or leaked card details, obtained through data breaches, phishing emails or purchased on the dark web.
Counterfeit cards
Fake or counterfeit cards are created using information illegally obtained by ‘skimming’ card data using a hidden device placed on an ATM or card reader.
Lost or stolen card
This type of card payment fraud involves the illegal use of a legitimate credit card, intercepted in the mail, pickpocketed or discovered and used without permission.
Card testing is fraud involving small sums and a danger signal of likely high-value card payment fraud to follow. A series of small, test payments often targeting companies that do not sell physical goods, or charity organisations that accept donations with no minimum limits and require little information, may lead to the loss of larger amounts if left unchecked.
Fraud as a Service (FaaS)
Much like solution service models designed for the legitimate digital economy, criminals are now monetising online fraud services. Fraud as a Service (FaaS) delivers a range of fraud tactics, tools, data and illicit collaborations.
Professional refunder
A growing number of ads on social media and web forums offer to return items and obtain refunds or achieve large discounts on behalf of a customer in exchange for a handling fee. These ‘professional refunders’ operate individually and in organised groups to facilitate scam refunds in volume.
These criminals target unwary merchants and their return policies, study procedures and dispute processes to take advantage of vulnerabilities and loopholes. Armed with legitimate order information provided by real customers, fraudsters apply for refunds intending to recoup the cost without returning the item, often reselling the item for profit. If the scam fails, the fraudster has the backup option of filing a chargeback.
Fake returns
This scam seeks to take advantage of weaknesses in warehouse processes and return procedures. Fake return fraud includes simply shipping an envelope with the return shipping label, sending an item of similar size and weight, or returning duplicate counterfeit items of inferior quality. Fraudsters may simply rely on return policies triggering as soon as a record of return is generated or seek to escalate a claim that the vendor delivered a fake or inferior item.
Most fake returns can be avoided by designing a returns policy that discourages abuse and promotes things like store credit, offering customers flexibility while protecting the business from scams.
Friendly fraud
The global pandemic and economic downturn have combined to increase opportunistic consumer fraud that seeks to recoup costs at a retailers’ expense. Merchants rushed to expand eCommerce without robust policies, socially distanced deliveries without signature were harder to prove, while demands on warehouses and couriers have stretched supply lead times causing delays and confusion.
Friendly fraud takes advantage of the very policies designed to protect customers from real scams or problems with products and services. Customers who initiate a legitimate refund can experience just how easy the process is, sometimes leading to further illegitimate claims and the alternative term ‘armchair fraud’ to describe this low-effort scam.
Chargeback fraud
Chargeback fraud, or credit card dispute fraud is a deliberate attempt by a cardholder to make an illegitimate chargeback to the card following an online purchase. The most common dispute reasons cited by cardholders include
- The charge or payee on the card statement is not recognised
- The product or service has not been received
- The product or service was defective, damaged, or not as described.
- The card was stolen or used without consent
The cost of credit card disputes impacts businesses in delivery, investigation and chargeback fees, but high transaction-to-chargeback ratios can also lead to additional consumer penalties. Card issuers are likely to increase chargeback fees and penalties and potentially limit card access.
Get insights from multiple channels for better fraud detection

Best strategies to beat transaction fraud
Start at customer onboarding
The battle to beat fraud begins at the point of customer onboarding, from the first customer interaction. Best practice in transaction fraud prevention recognises risk at the earliest possible stage by collaborating with onboarding teams and in-life customer monitoring teams, ensuring that these teams are well-equipped to deliver a targeted transaction monitoring strategy.
Creating a feedback loop between onboarding and transaction events enables end-to-end customer risk mitigation across the customer lifecycle. Instead of treating them as discrete activities, an integrated approach to fraud management including both customer onboarding insights and transaction events allows for a more holistic view of the changing risk assessment of a customer relationship. This more complete approach is useful in adjusting risk assessment as a customer seeks to add more services and the relationship changes and grows.
End-to-end customer risk mitigation
✓ Provides one complete customer view of risk
✓ Monitoring is driven by individual customer risk
✓ More accurate decisions using data from across the customer lifecycle
✓ Reduced service friction and improved customer experience
Take a risk-based approach
Risk assessment is more than regulatory compliance. A risk-based approach to transactions achieves more targeted, efficient and effective transaction monitoring.
A risk-based approach does not need to cover every scenario but should be sufficient to understand each product or service and sales channel. Begin by defining a baseline set of procedure policies and rules for each product or service your business offers. Grouping products where there is sufficient crossover will deliver more efficient procedure policies. By segmenting customers, products and services in this way, a business can carry out bespoke, transaction monitoring, focussing operational resources and delivering a better customer experience.
“A risk-based approach to transactions achieves more targeted, efficient and effective transaction monitoring.”
Layer components and refine the process
Configurable workflows, scorecards, rules and adaptive rules, fuzzy matching algorithms, ML models, profiling and behavioural analysis, reference tables, data orchestration, watchlists – the fraud detection toolbox contains an extensive choice of detection and prevention components.
Good fraud detection relies on the combination and careful calibration of these components rather than one ‘killer app’. Transaction monitoring especially requires process refinement to reduce noise and false positives; each component should add value and the order in which components are deployed also matters. So, successful transaction monitoring is not the sum of its parts but an iterative process to achieve optimal detection and alert volume based on the business’ approach to risk.
Detect and act on potential fraudulent threats with GBG Predator

How to detect transaction fraud
Transaction monitoring solutions provide real-time, rule-based protection from fraudulent activity, sifting and evaluating transaction events and triggering risk alerts when those transactions require review. These solutions are designed to support a risk-based approach to fraud prevention, automating decisions wherever possible, reducing manual overhead and limiting the number of false positive alerts.
Here are five key considerations to drive an effective transaction filtering process and produce high-value and high-quality alerts.
Configuration and profiling
Choosing a fraud prevention solution that provides a business-level, intuitive interface to build, test and refine detection strategies is a must. With the fast-evolving nature of fraud, every second counts.
Configurable calculations or machine learning models designed to detect anomalous behaviour all form pattern analysis known as ‘profiling’. Accurate profiling allows for a more comprehensive view of transactions, rather than focussing on discrete triggering events. Profiling takes into account individual customer behaviour and the intricacies and differences in personal circumstances and events resulting in better anomaly detection and reduced false positives.
Alternative data and fraud signals
Traditional methods of transaction monitoring based on limited transaction data points are no longer enough to accurately signal fraud and suspicious behaviour. Location, email, mobile intelligence, social media, device and behavioural biometrics form a growing list of additional fraud signals available from alternative data.
Businesses combining transaction data with this supplementary data intelligence can construct a richer, contextual understanding of individual consumers, delivering more accurate risk assessment and more personalised customer experiences.
Network analytics
Network analytics or ‘data consortiums’ are now a key component used to provide additional fraud insights, allowing businesses to map and understand customer behaviour beyond their own interactions with them.
The digital world is now host to many sites and services, customers and the interconnecting relationships between them. Understanding these networks and the reputation of the digital identities that pop up in different places allows businesses to leverage shared intelligence, whilst still preserving the privacy of the individuals that are represented by those digital identities.
Make machine learning count
Machine learning is no substitute for standard rules-based systems, but it is a powerful complementary component in transaction fraud detection. Sifting through high volumes of data and providing greater speed and accuracy, machine learning can eliminate manual, time-consuming tasks and enable efficient business scaling. With supervised, unsupervised and custom models now common, fraud analysts can leverage a growing list of ensemble algorithms and collaborative models that leave them free to focus attention on critical, high-value cases.
Customers benefit from fast processing, reduced friction and greater protection from fraud while enhanced risk mitigation for business make investment in machine learning a compelling proposition.
Machine learning
✓ Easily manages high volumes of complex data
✓ Delivers high accuracy with low false positives
✓ Effective detection of emerging fraud typologies
✓ Frees up fraud analyst time for high-value work
Intuitive case management
Once a fraud prevention solution flags a transaction, investigation teams benefit from intuitive case management functionality to review important details and make quick and accurate decisions. The best solutions support individual user control and team collaboration, with case triage, assignment, notes and audit creation, visual link analysis of alerts all useful features for case management.
An automated solution that is optimally configured to reduce false positive fraud alerts, can be supported by a small team of skilled analysts with the experience, intuition, and insights to quickly carry out remediation and investigation activity. Systems that are poorly configured will produce a greater number of false positives and this will require more manual processing. Whereas good systems scale easily with the volume of digital transactions; poor systems don’t, requiring increasing amounts of manual investigative effort.
Frequently asked questions
What is transaction fraud?
Transaction fraud is a risk for any business trading online. It describes the attempt to deliberately seek to gain financial or other personal gain through wrongful or criminal deception. This might include the misappropriation of identity or payment methods or the misrepresentation of information by a fraudster or a customer.
What is an authorised push payment?
Authorised push payment fraud involves the ‘social engineering’ of a victim to send a payment to an account controlled by the criminal. Posing as a legitimate authority, such as, a government department, bank or debt collection agency. The fraudster creates a false sense of urgency intended to elicit an immediate payment in response.
What is account takeover?
Account takeover is a type of identity theft and a very common type of transaction fraud. It hinges on the theft or interception of personal account credentials, security questions and other data useful to gain access to and control over a victim’s account.
How can I detect transaction fraud?
Detecting transaction fraud in today’s digital economy demands automated solutions and expert fraud analysts. A business must be able to sift transaction events, segregate and identify suspicious activities or anomalies and generate accurate, efficient and timely feedback on the analysis of transactions.
Sign up for more expert insight
Hear from us when we launch new research, guides and reports.