
Tackling fraud with physical tamper detection
Recaptured images and face substitution are a challenge for any business that uses remote identity verification because they’re hard to spot with the naked eye. GBG IDscan reveals recaptured images to help business fight identity fraud.
If you open a bank account in 2020, you may not need to visit a branch in person to prove your identity. Instead, you’ll be asked to hold an official identity document up to your mobile camera or webcam. The entire identity verification process is completely online and the party verifying the identity has no access to the physical version of the document.
Organisations need to automatically verify if the photograph represents a genuine identity document or a faked one (for example, a fake identity document simply printed on a piece of paper, or on a screen). The latter is where recapturing comes into play.
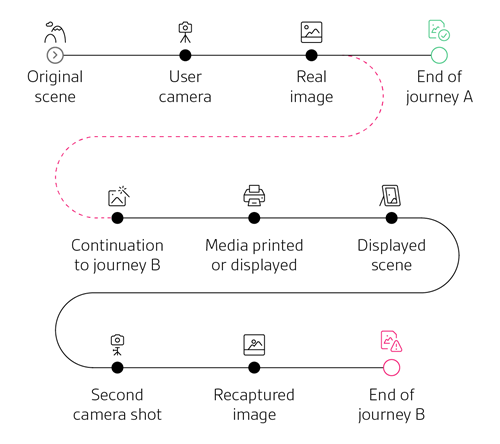
How it works
It works like this: A fraudster prints a digital image using an inkjet/laser printer, or displays it on a screen/projector, and then takes a photo or video of it with a camera.
Casual counterfeiters rely on inkjet/laser printers and paper to mimic the genuine documents. They capture a photograph of a genuine document (or download it), digitally manipulate it and print it. This is a simple and inexpensive process to produce fake identity documents. Finally, they hold up the newly created document to the mobile camera or webcam to fool identity document verification systems.
It’s difficult for the human eye to distinguish between such pictures and genuine identity documents. For instance, Fig. 2 shows six identity cards. All of them are counterfeit and printed by a casual inkjet or laser printer on paper.

Crucially, a photo of a printed/displayed digitally tampered image does not contain any traces of digital tampering because it’s a genuine digital image. Therefore, detecting recaptured images is key to fraud prevention.
Recaptured identity cards printed on paper often exhibit distinguishable artefacts such as blurriness, noise, colour imperfection, etc.
However, the big challenge is that real-life images of genuine ID documents obtained in uncontrolled environments also often exhibit similar artefacts. For instance, Fig. 3, shows pictures of characters extracted from images of real identity cards and recaptured ones (printed on paper).
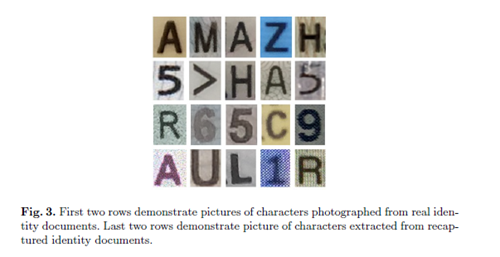
The first two rows show characters extracted from genuine documents and the bottom two show characters extracted from recaptured documents. It can be a challenge to tell them apart.
GBG IDscan physical tamper technology uses a local approach based on machine learning. It identities feature and noise levels of regions that correspond to printed characters and detects whether the image is an authentic physical ID document or a recapture on paper or a screen.
Detecting portrait photo substitution
Some fraudsters will physically replace the photograph on a genuine identity document with another to masquerade as the bona fide holder of the document. There are many challenges when it comes to detecting photo substitutions (Fig 4).
For example, any solution has to account for large intra-class diversity (background, watermark, ethnicities, etc.), varying lighting conditions (day, night, exterior, interior, etc.) and image quality (camera, compression, blur, etc.)

Using both a traditional and a deep-learning-based approach, GBG IDscan portrait photo substitution and alerts users.
Find out more about digital document verification or get in touch to learn more about GBG IDscan’s physical tampering detection capabilities.
Build trust & confidence
Our ability to layer documents with data gives you a 100% decision rate and the most effective solution in the market.